Azure KeyVault and Extensible Key Management
I’ve been reading up on Azure KeyVault, and the more I read about it the more I like it. There is a Technet blog that posts news and other pieces of information. There’s even a forum for feedback and discussions.
Utilising Azure KeyVault in SQL Server means that for Extensible Key Management you can now replace the need for a certificate stored in master with a key stored in the Azure Key Vault. The certificate Encryption Key Hierarchy is usually used for Transparent Data Encryption, Column Level Encryption and Encrypted Backups. Pretty picture provided by Microsoft.
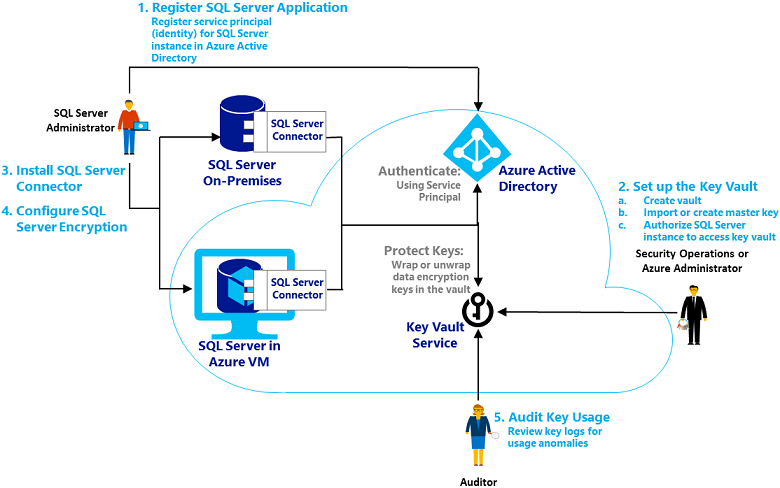
This now means that the keys are kept apart which was never the case previously as sysadmin had access to everything, But now as you can see that not only are the keys apart, but the role of creating them are also separate tasks ran by separate people.
To play around with the Key Vault, you can follow this blog post.
If you’d rather work using Azure PowerShell, then follow this Azure how-to. Full cmdlets are available on MSDN.